Most teams discover AI agents are risky during a messy rollout, not from a tidy design review. Working across different tech companies, we have seen agents exfiltrate data via over-privileged tools, expose embeddings from misconfigured vector databases, and trigger SSRF through third-party plugins. You think you know your controls until a prompt-injected agent chains a few APIs and bypasses your guardrails. The average breach reached $4.44M in 2025 per IBM's Cost of a Data Breach, and AI incidents are rising, which makes threat modeling for agentic systems a must, not a nice-to-have.
Gartner projects information security end-user spending to hit $244B in 2026 and warns that by 2027, 17 percent of cyberattacks will involve GenAI, underscoring demand for secure-by-design practices in AI and app security (Gartner press release, Jul 29, 2025).
ThreatModeler
Intelligent, automated threat modeling for applications, cloud, and infrastructure.
One-click cloud imports, diagramming, and rule-driven threats that tie into dev and security workflows.
Best for: Large product, platform, and cloud teams that need portfolio-scale modeling tied to SDLC tooling.
Key Features:
- CloudModeler style one-click import and sync for AWS architectures, plus built-in compliance mappings, per the AWS Marketplace listing for ThreatModeler.
- Integrations noted for CI/CD and ALM systems like Jira and Jenkins, along with reporting that communicates risks to stakeholders (AWS Marketplace listing).
- Model chaining to reuse components and keep patterns consistent across systems.
Why we like it: From our experience in the startup ecosystem, teams adopt it when whiteboards break down. Automatic cloud imports plus reusable models help you standardize reviews without slowing delivery.
Notable Limitations:
- Reviewers mention UI quirks like connector layout and comment layering that can hamper complex diagrams (PeerSpot reviews).
- Pricing and consumption details are opaque unless you work through sales or a marketplace contract.
Pricing: Pricing not publicly available in simple tiers. Available via contract on AWS Marketplace; verify terms with your reseller or vendor.
IriusRisk
AI-fused threat modeling for secure design, with libraries of threats and countermeasures.
Drag-and-drop diagrams, requirements, and integrations to move security left.
Best for: Enterprises standardizing threat modeling, compliance mapping, and Jira or Azure DevOps workflows across many teams.
Key Features:
- Two-way sync with ALM tools and predefined standards coverage such as OWASP ASVS and NIST 800-53, per the AWS Marketplace listing.
- Reviewers highlight fast generation of threat models and countermeasures to reduce delays to production (G2 reviews).
- Documented on Gartner Peer Insights as supporting automated security requirements and SDLC integration (Gartner Peer Insights).
Why we like it: After helping startups scale, we have seen IriusRisk succeed when you need consistent, repeatable modeling at portfolio scale with traceability into backlogs.
Notable Limitations:
- Users cite an outdated UI feel, integration effort, and confusing licensing in some environments.
- Performance can lag on very large models per individual reviewer feedback.
Pricing: Publicly listed from $35,000 for 12 months including 5 threat models on AWS Marketplace. Larger deployments are contract-based.
Devici
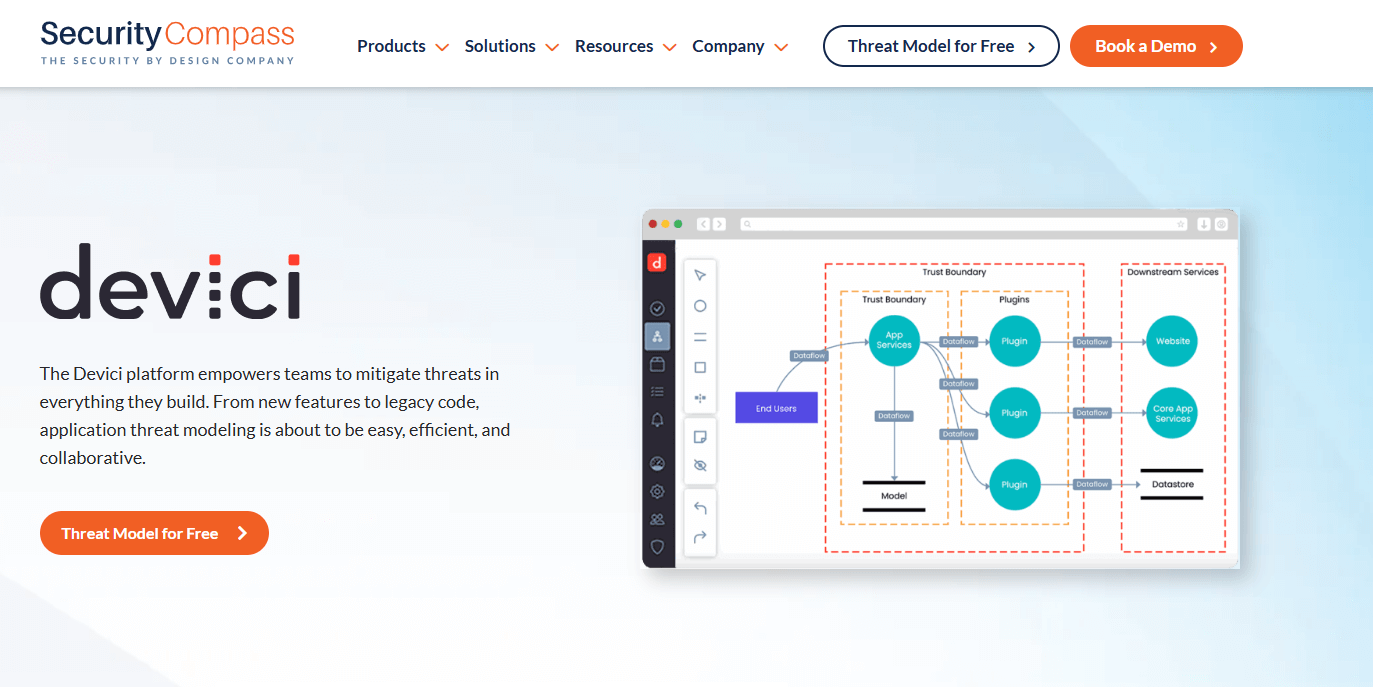
Diagram-driven, AI-infused threat modeling with code-to-model automation and a collaborative canvas.
Now part of Security Compass, complements SD Elements with a modern modeling UX.
Best for: Product and platform teams that want a lightweight, collaborative modeling canvas with AI assistance, plus an easy on-ramp for non-security roles.
Key Features:
- Acquisition by Security Compass (June 2025) expands DevSecOps coverage, confirming Devici's diagram-first approach and developer focus (ChannelE2E coverage).
- Security Compass announced expanded AI security content and repo scanning in SD Elements, which pairs well with Devici for broader secure-by-design programs (Business Wire release).
- Rich content coverage for AI topics like OWASP Agentic AI threats, NIST AI RMF, and OWASP LLM Top 10, per Security Compass materials cited in third-party coverage.
Why we like it: Working across different tech companies, we have found the collaborative canvas lowers the barrier for architects and PMs. It is a practical way to get agent design risks discussed early.
Notable Limitations:
- Acquired in mid-2025 and integrated under Security Compass, so roadmap, packaging, and support paths may evolve; independent third-party reviews remain limited as of early 2026.
- Feature depth for heavy compliance programs is typically addressed in tandem with SD Elements, which can add evaluation scope (Gartner Peer Insights page for SD Elements).
Pricing: Per vendor documentation, a free plan exists for small teams (up to 3 threat models), with Pro and Enterprise on request. No independent third-party price sheets as of publication.
Prisma AIRS
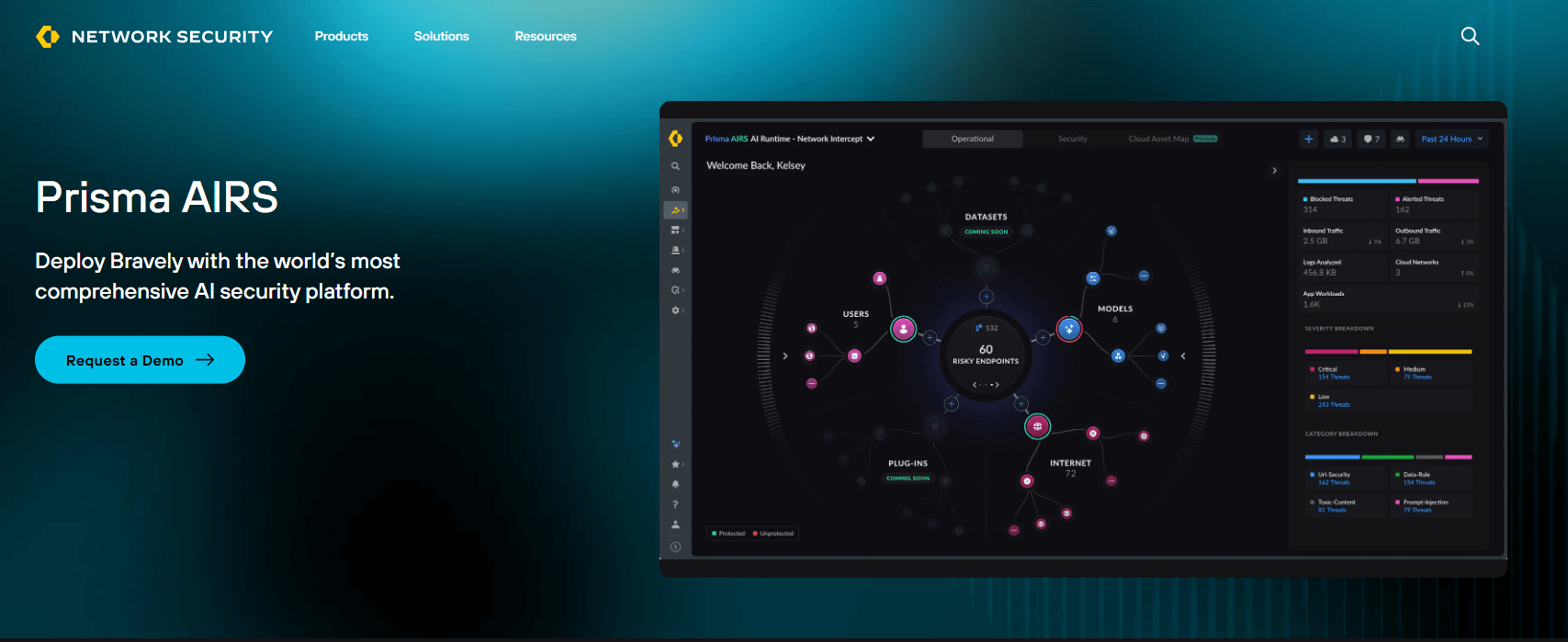
Comprehensive AI runtime security that protects AI agents, models, data, and applications.
Focuses on prompt injection, tool misuse, data loss, and other agentic runtime threats.
Best for: Security teams that need runtime controls for LLM apps and agents to complement design-time threat modeling.
Key Features:
- Platform launched in April 2025 with capabilities including AI model scanning, posture management, red teaming, runtime security, and agent security. Prisma AIRS 2.0 shipped in October 2025, completing the native integration of the acquired Protect AI technology (Palo Alto Networks press release).
- API-based runtime inspection for prompt injection, sensitive data loss, malicious URLs, and tool misuse is listed on AWS Marketplace.
- Broader AI security strategy bolstered by the completed Protect AI acquisition (July 2025), with native integrations announced for Factory, Glean, IBM, and ServiceNow platforms.
Why we like it: Threat models are only half the story for agents. Prisma AIRS adds runtime detection and enforcement for agent actions, which is critical for OWASP LLM risks like prompt injection and excessive agency (AWS Prescriptive Guidance mapping).
Notable Limitations:
- Platform is maturing quickly post-acquisition; independent customer reviews are still growing as of early 2026.
- Air-gapped deployments are not publicly documented, and several features rely on cloud services and regional processing per product materials; confirm data residency and architecture in procurement.
Pricing: Public contract option on AWS Marketplace shows $4,353 for a 12-month API-call entitlement. Larger volumes and bundles are quote-based.
Agent Threat Modeling Tools Comparison: Quick Overview
| Tool | Best For | Pricing Model | Highlights |
|---|---|---|---|
| ThreatModeler | Enterprises standardizing cloud and app modeling | Contract or marketplace | One-click cloud imports, compliance mappings, SDLC integrations |
| IriusRisk | Portfolio-scale secure design and backlog integration | Contract, public SKU on AWS Marketplace | Two-way ALM sync, standards, countermeasures |
| Devici | Collaborative, AI-assisted modeling for cross-functional teams | Vendor-quoted (free plan available) | Diagram-first canvas, AI-assisted modeling, integrated under Security Compass |
| Prisma AIRS | Runtime protection for AI agents and LLM apps | Contract and AWS Marketplace | Detects prompt injection, data loss, tool misuse at runtime |
Agent Threat Modeling Platform Comparison: Key Features at a Glance
| Tool | Feature 1 | Feature 2 | Feature 3 |
|---|---|---|---|
| ThreatModeler | Cloud import and sync | Compliance mappings | CI/CD and ALM integrations |
| IriusRisk | Threat and countermeasure libraries | Two-way Jira/Azure DevOps | Standards coverage (OWASP ASVS, NIST 800-53) |
| Devici | Diagram-driven modeling | AI-assisted attributes and content | Security Compass portfolio alignment |
| Prisma AIRS | Runtime inspection API | Prompt injection and SSDL detection | Agent tool-misuse controls |
Agent Threat Modeling Deployment Options
| Tool | Cloud API | On-Premise | Integration Complexity |
|---|---|---|---|
| ThreatModeler | Yes, SaaS and AWS CFT delivery | Self-host in your VPC per listing | Medium, ties to CI/CD and ALM |
| IriusRisk | Yes, SaaS | On-prem options discussed in documentation and releases | Medium, ALM integrations |
| Devici | Yes | Not publicly documented | Low, collaborative canvas |
| Prisma AIRS | Yes, API via AWS Marketplace | Not publicly documented | Medium to High, ties into broader platform |
Agent Threat Modeling Strategic Decision Framework
| Critical Question | Why It Matters | What to Evaluate | Red Flags |
|---|---|---|---|
| Do we model agent tool use and data flows explicitly? | Agent attacks often ride tool chains and plugins | Diagram fidelity, countermeasure libraries for agentic risks | Only code-scanner style checks, no agent design focus |
| Can we connect models to backlogs? | Findings must turn into tracked work | Jira/Azure DevOps sync, requirement templates | PDF reports without synchronization |
| Do we need runtime agent controls? | OWASP lists prompt injection and excessive agency as top risks | API inspection, DLP, tool-misuse detection | No runtime path, design-time only |
| What is our deployment constraint? | Data residency and sovereignty affect SaaS choices | SaaS regions, on-prem options, logging | No clarity on data processing locations |
Agent Threat Modeling Solutions Comparison: Pricing & Capabilities Overview
| Organization Size | Recommended Setup | Annual Investment |
|---|---|---|
| Startup to Mid-market | Devici for collaborative modeling, add Prisma AIRS if shipping agentic apps | Prisma AIRS API entitlement listed at $4,353 per 12 months for a starter contract, others quote-based |
| Regulated Mid-market | IriusRisk with ALM sync, consider Prisma AIRS for runtime | IriusRisk listing starts at $35,000 per year for 5 models, larger scopes are contract-based |
| Large Enterprise | ThreatModeler or IriusRisk across portfolios, Prisma AIRS for runtime | Contract-based, often through marketplaces or enterprise agreements |
Problems & Solutions
-
Problem: Prompt injection and excessive agency in LLM agents
- Context: OWASP's 2025 lists prompt injection and excessive agency among the top LLM risks, echoed by AWS prescriptive guidance mapping controls to the OWASP list (OWASP via Invicti, AWS Prescriptive Guidance). The UK NCSC also warns prompt injection may never be fully mitigated, which underscores the need for layered defenses (TechRadar).
- How tools help:
- ThreatModeler and IriusRisk, with threat libraries and standards mappings, help you design out risky agent behaviors and enforce least privilege early.
- Devici's collaborative canvases help non-security roles see tool chains that create excessive agency, improving remediation planning.
- Prisma AIRS adds runtime inspection to block prompt injection attempts, sensitive data loss, and tool misuse.
-
Problem: Indirect prompt injection through data sources and plugins
- Context: Indirect or second-order injections can hijack higher-privileged agents through malicious content or cross-agent workflows (TechRadar).
- How tools help:
- IriusRisk and ThreatModeler can model data lineage and plugin trust boundaries to document compensating controls and test points.
- Prisma AIRS monitors inputs and outputs at runtime to detect malicious URLs, code, and injections across agent chains.
-
Problem: Proving ROI of secure-by-design for boards
- Context: With breach costs sustained and AI raising stakes, boards demand quantifiable security outcomes (IBM 2025 breach analysis).
- How tools help:
- ThreatModeler and IriusRisk both connect threats to requirements and backlogs so you can show remediation progress and compliance coverage in reports.
- Devici makes early modeling accessible, improving participation and speeding up reviews, which reduces late-stage rework.
- Prisma AIRS provides runtime event data, which gives SOC and leadership proof of blocked agent threats.
Bottom Line: Pick for Design First, Add Runtime Where Agents Matter
For AI agent programs, combine design-time threat modeling with runtime controls. Use ThreatModeler or IriusRisk to standardize diagrams, threats, and countermeasures across teams, then add Prisma AIRS when you put autonomous or tool-using agents into production. If your culture needs a collaborative, lower-friction start, Devici's canvas is a smart on-ramp, especially now that it sits within a broader secure-by-design suite at Security Compass. Given Gartner's forecast on GenAI-linked attacks and the sustained cost of breaches, prioritizing agent-aware threat modeling now pays off in resilience and audit-ready evidence by design.


