Most teams discover overexposed sensitive data during breach triage, not from quarterly audits. Working across different tech companies, I have watched cloud data sprawl create real risk, for example a public object store holding customer PII, a Snowflake role that inherits excessive warehouse privileges, or an OAuth token with broad scopes pulling regulated data into a shadow SaaS. By 2026, breach cost studies continue to show the global average breach cost hovering around five million dollars, reinforcing that closing data exposure paths is not optional. As data estates grow more distributed across cloud, SaaS, and analytics platforms, the speed at which teams can identify, prioritize, and remediate exposed sensitive data has become a core security capability rather than a compliance exercise.
Wiz DSPM
Agentless CNAPP with integrated DSPM that discovers and classifies sensitive cloud data, correlates risks on a security graph, and prioritizes attack paths to critical data. Adds context from identities, vulnerabilities, exposure, and runtime signals to drive remediation.
- Best for: Cloud‑first teams that want DSPM embedded in a broader CNAPP and attack‑path context across AWS, Azure, and GCP.
- Key Features: Agentless discovery and data classification, attack‑path analysis to "crown‑jewel" data, identity and exposure correlation, compliance mapping, and runtime signal ingestion.
- Why we like it: The security graph makes DSPM findings immediately actionable by tying data exposure to exploitable paths, which cuts noise and accelerates fixes.
- Notable Limitations: Buyers report a need for stronger out‑of‑the‑box executive reporting and deeper workflow automation, and some note API integrations require tuning. These themes show up in community reviews on PeerSpot and similar outlets.
- Pricing: AWS Marketplace lists Wiz Essential at $24,000 per year for 100 workloads and Wiz Advanced at $38,000 per year for 100 workloads, with add‑ons for sensors and code scanning. See the published tiers on the AWS Marketplace listing. Independent ratings show strong satisfaction on Gartner Peer Insights for CSPM and CNAPP, which many teams pair with DSPM inside Wiz (Gartner Peer Insights vendor page).
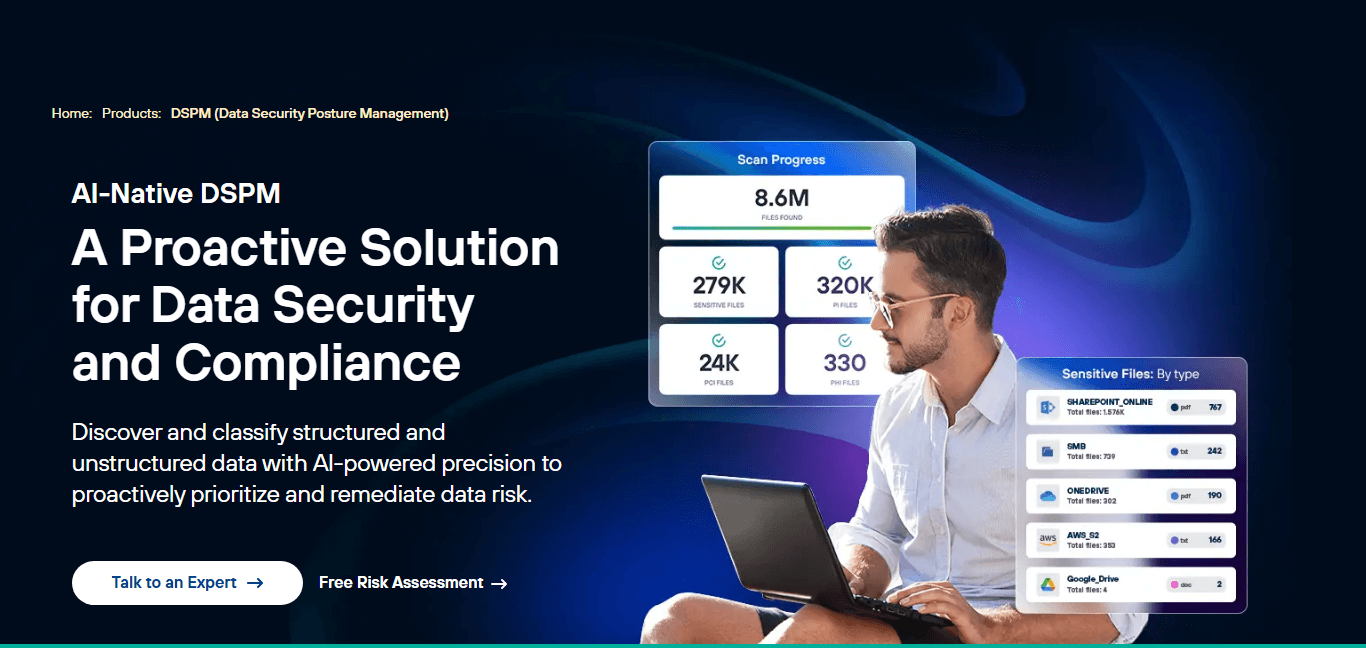
Cyera DSPM
AI‑native DSPM that continuously discovers, classifies, and secures critical data across cloud, SaaS, and on‑prem environments with agentless deployment. Recent releases add on‑prem databases and file shares and incident response services.
- Best for: Enterprises that want rapid, AI‑driven discovery across hybrid estates, including SaaS and expanding on‑prem coverage.
- Key Features: Continuous discovery and classification, risk‑based findings with remediation guidance, identity‑to‑data context, on‑prem connectors for databases and file shares, and incident response offerings.
- Why we like it: Coverage growth has been fast, with strong market momentum and scale, which matters when you need to scan large estates quickly during investigations.
- Notable Limitations: Earlier customer feedback noted limited on‑prem support and configuration constraints, though recent releases address on‑prem gaps. You can see this evolution reflected in third‑party feedback on G2.
- Pricing: Pricing not publicly available. Contact Cyera for a custom quote. Funding and growth context: Cyera raised $300M at $3B valuation in November 2024, then $540M at $6B valuation in June 2025, demonstrating category momentum and investor confidence in the DSPM space. On‑prem expansion announcements were covered by outlets like TDWI.
Symmetry Systems DataGuard
Object‑level lineage DSPM for cloud object stores and databases that models data permissions and flows, with options for strict environments. Notable for deployments where data must stay "in your cloud," including air‑gapped scenarios.
- Best for: Regulated and high‑assurance environments that need "in‑customer‑cloud," hybrid, or air‑gapped DSPM deployments.
- Key Features: Object‑level data inventory and lineage, identity‑to‑data permissions graph, hybrid cloud coverage, SIEM integrations, and support for air‑gapped deployment.
- Why we like it: The ability to deploy in air‑gapped environments is rare in this category, and object‑level lineage helps teams answer who can access what with precision.
- Notable Limitations: Public hands‑on reviews are fewer than larger CNAPP suites, so buyers should request customer references and a proof‑of‑value in their own environment. Gartner Peer Insights shows a smaller but positive review base.
- Pricing: Pricing not publicly available. Contact Symmetry Systems for a custom quote. Recognition items include Strong Performer placement in Gartner's Voice of the Customer for DSPM as reported via PRNewswire and the company's air‑gapped deployment announcement covered on PRNewswire.
Varonis Data Security
DSPM capabilities as part of a broader data security platform that automatically classifies sensitive data, monitors user behavior and permissions, and orchestrates remediation across SaaS, cloud, and on‑prem.
- Best for: Teams that want DSPM tied to mature data access governance and behavior analytics across SaaS and data platforms.
- Key Features: Automated discovery and classification, real‑time threat detection, permission right‑sizing, automated remediation workflows, Snowflake coverage, and broad SaaS connectors.
- Why we like it: Strong remediation and governance features reduce exposure and drive measurable permission cleanup, not just reports.
- Notable Limitations: Reviews frequently mention higher cost and a learning curve during initial rollout, especially in large environments. See buyer feedback on G2.
- Pricing: AWS Marketplace lists published annual rates per integration, for example "Varonis for AWS/S3/RDS IaaS" from $750 and popular SaaS connectors from $310 to $400 per year per listing unit. Real spend depends on scope and private offers. Verify current prices on the AWS Marketplace listing. Product expansion to Snowflake DSPM was announced via GlobeNewswire.
Open Raven DSPM
Open‑architecture DSPM known for cloud API integrations and analyzing data in place, with an emphasis on customizable scanning and policy. As of June 11, 2024, Open Raven was acquired by Formstack and continues as part of that platform.
- Best for: Teams that want predictable, in‑place cloud data scanning and are comfortable with a product now nested inside a workflow vendor.
- Key Features: API‑driven discovery and classification at cloud scale, data detection and response, and flexible controls for scan scope and budgets.
- Why we like it: The platform's in‑place analysis model and predictable scanning controls have appealed to teams that must balance fidelity with cloud‑cost guardrails.
- Notable Limitations: Limited public reviews compared to peers and a user‑reported desire for a more intuitive UI. Roadmap priority may change under new ownership. See acquisition coverage on Business Wire and sparse buyer reviews on G2.
- Pricing: AWS Marketplace lists a Standard plan at $50,000 per year. Confirm latest terms on the AWS Marketplace listing.
Forcepoint DSPM
DSPM delivered within a broader data security portfolio with DLP, DDR, SSE, and email, recently expanded through the acquisition of Getvisibility and new releases focused on structured and unstructured data.
- Best for: Organizations standardizing on Forcepoint for DLP and SSE that want unified data security, posture, and enforcement.
- Key Features: AI‑driven discovery and classification, data risk insights, remediation workflows, integration with DLP and SSE, and support for structured data sources.
- Why we like it: A single‑policy approach across DSPM and DLP reduces duplicate policies and helps teams move from visibility to enforcement.
- Notable Limitations: DSPM is newer than its DLP suite, and public DSPM reviews are fewer, so validate coverage of your specific data stores and the depth of automated fixes. Gartner Peer Insights shows early but growing review counts for DSPM.
- Pricing: DSPM pricing not publicly posted. Contact Forcepoint for a custom quote. Related Forcepoint add‑ons on AWS Marketplace provide pricing signals, for example Cloud Security Posture Management add‑ons at $10,000 per account per year within Forcepoint ONE, see AWS Marketplace. Forcepoint's 2025 acquisition of Getvisibility is noted in industry communications and aligns with its data security strategy (Gartner Peer Insights vendor page).
Data Security Posture Management Tools Comparison: Quick Overview
| Tool | Best For | Pricing Model | Highlights |
|---|---|---|---|
| Wiz DSPM | Cloud‑first teams wanting CNAPP plus DSPM | Subscription, published tiers on AWS Marketplace | Strong attack‑path context to sensitive data, high peer ratings |
| Cyera DSPM | Hybrid estates, rapid discovery across cloud, SaaS, on‑prem | Enterprise subscription | Fast coverage growth, $6B valuation as of June 2025 |
| Symmetry Systems DataGuard | Regulated, high‑assurance, or air‑gapped deployments | Enterprise subscription | Air‑gapped DSPM option |
| Varonis Data Security | DSPM tied to data governance and behavior analytics | Subscription, connectors listed on AWS Marketplace | Automated remediation and governance, Snowflake DSPM |
| Open Raven DSPM | Cloud data scanning in place with predictable controls | Subscription, AWS Marketplace | Acquired by Formstack, Standard plan published on Marketplace |
| Forcepoint DSPM | Unified data security with DLP and SSE | Enterprise subscription | Expanded via Getvisibility acquisition, unified policy strategy |
Data Security Posture Management Platform Comparison: Key Features at a Glance
| Tool | Sensitive Data Discovery | Attack‑Path/Context | Identity‑to‑Data Mapping |
|---|---|---|---|
| Wiz DSPM | Yes | Yes, security graph and attack‑path focus | Yes |
| Cyera DSPM | Yes | Yes, risk‑based findings | Yes |
| Symmetry Systems DataGuard | Yes | Emphasis on object‑level lineage | Yes, permissions graph |
| Varonis Data Security | Yes | Yes, with governance and threat context | Yes |
| Open Raven DSPM | Yes | Risk and policy context | Limited public detail |
| Forcepoint DSPM | Yes | Risk insights with DLP and SSE context | Yes |
Data Security Posture Management Deployment Options
| Tool | Cloud API | On‑Premise | Air‑Gapped | Integration Complexity |
|---|---|---|---|---|
| Wiz DSPM | Yes | Limited, primarily SaaS/cloud‑API | No | Low, agentless |
| Cyera DSPM | Yes | Yes, on‑prem databases and file shares | No | Low, connector‑based |
| Symmetry Systems DataGuard | Yes | Yes | Yes | Moderate, unique option for strict environments |
| Varonis Data Security | Yes | Yes | Not advertised | Moderate, broad connector mix |
| Open Raven DSPM | Yes | Limited public detail | Not advertised | Low to moderate, API‑first |
| Forcepoint DSPM | Yes | Yes | Not advertised | Moderate, unified with DLP/SSE |
Data Security Posture Management Strategic Decision Framework
| Critical Question | Why It Matters | What to Evaluate | Red Flags |
|---|---|---|---|
| Can the tool prioritize exposure paths to crown‑jewel data, not just list mislabels? | Cuts remediation time and breach risk | Attack‑path correlation to identities, vulnerabilities, and data | CSV‑style reports with no context or fix path |
| Do you need on‑prem or air‑gapped options? | Regulated workloads might prohibit SaaS scanning | Supported databases, deployment models, data egress model | "Cloud only" answers when sovereignty is a hard constraint |
| How well does it remediate excessive permissions and data oversharing? | DSPM that stops at visibility leaves risk | Automated permission right‑sizing, bulk share link cleanup, policy workflows | Manual ticket sprawl, little or no write‑back |
| What is the total platform fit? | Many teams consolidate DSPM with CNAPP or DLP | Native tie‑ins to CNAPP, DLP, SSE, and IR playbooks | Point tool that duplicates existing controls |
Data Security Posture Management Solutions Comparison: Pricing & Capabilities Overview
| Organization Size | Recommended Setup | Annual Investment | Notes |
|---|---|---|---|
| 200–500 employees, cloud‑first | Wiz Essential or Advanced with DSPM features, or Cyera starter scope | Example: Wiz Advanced is $38,000 per year for 100 workloads | Varies by private offer |
| 500–5,000 employees, hybrid | Cyera or Varonis for hybrid SaaS plus data stores, Symmetry for strict control needs | Varonis connectors from $310–$750 per year per connector | Actual totals depend on scope |
| 5,000+ employees, consolidation | Forcepoint DSPM with DLP and SSE, Wiz CNAPP plus DSPM, or mixed stack | Forcepoint posture add‑ons at $10,000 per account per year | DSPM is custom‑quoted |
Problems & Solutions
-
Problem: Shadow data in multi‑cloud leads to breach impact and long investigations.
- Wiz correlates sensitive data to exploitable attack paths, which helps teams fix the real exposure first, a workflow echoed in peer feedback on PeerSpot.
- Cyera has emphasized fast time to value at scale and has raised significant capital to expand coverage, reflecting demand to scan large estates quickly.
- Open Raven scans data in place with API integrations and has predictable scanning controls, which users cite as helpful for cost management, with pricing transparency on AWS Marketplace.
-
Problem: SaaS oversharing and Snowflake sprawl create compliance exposure.
- Varonis expanded DSPM to Snowflake and pairs it with permission right‑sizing and threat detection, reducing the noisy share links and over‑entitled roles that auditors flag (reviewer themes on G2).
- Wiz and Cyera both classify sensitive data across popular SaaS platforms, then tie findings to identities and exposures, which reviewers and industry coverage describe as critical to cleanup.
-
Problem: Regulated workloads require strict custody or even air‑gapped operations.
- Symmetry Systems announced air‑gapped DSPM deployments, a differentiator for classified or disconnected networks.
- Forcepoint's portfolio approach lets teams unify DSPM with DLP and SSE policies to keep controls local and auditable, with early DSPM listings reflected on Gartner Peer Insights and posture add‑ons priced in AWS Marketplace.
-
Problem: Post‑incident scoping, "what data was touched," delays reporting and recovery.
- Cyera launched an incident response service that leans on its discovery and context to speed scoping and materiality analysis, reported via PRNewswire.
- Wiz's graph and attack‑path context, highlighted in user reviews, help teams triage where data exposure is plausible and where to contain first.
- Varonis users frequently cite automated responses and investigations in reviews, which reduce the manual steps to answer who accessed what and when.
Bottom Line: Pick for Coverage, Context, and the Fix
Breach costs remain stubbornly high, with the average incident still costing organizations around five million dollars globally, and a growing share of those incidents tied to sensitive data spread across cloud, SaaS, and analytics platforms. By 2026, most security leaders recognize that visibility alone is not enough. DSPM platforms must provide context, prioritize real exposure paths, and drive remediation that actually reduces blast radius.
If you want cloud security posture and attack path context tightly coupled with DSPM, Wiz is a strong starting point. If your challenge is rapid discovery across hybrid environments with growing on prem and SaaS scope, Cyera is worth shortlisting. If you operate in regulated or restricted environments that require in customer cloud or air gapped deployment, Symmetry Systems stands out. If governance, permission cleanup, and automated remediation are priorities, Varonis remains a proven option. If you are consolidating DSPM with DLP and SSE under one policy framework, Forcepoint’s platform approach can simplify enforcement. Open Raven fits teams that value in place scanning and predictable controls, with the caveat that it now sits inside a broader workflow vendor.
Use the framework in this guide to pressure test each option on three dimensions: coverage of where your data actually lives, context that ties exposure to real risk, and the ability to fix issues at scale without creating ticket sprawl. That is what separates DSPM that looks good in reports from DSPM that materially reduces breach impact in 2026.


