You think you know least privilege until your always-on agent chains five tool calls at 2 a.m. and writes to production. From our experience in the startup ecosystem, the biggest misses happen when teams assume RBAC is enough and skip runtime controls. According to IBM's Cost of a Data Breach 2025, the global average breach reached $4.44 million - down from $4.88 million the year prior, though U.S. costs climbed to $10.22 million - which is why teams now treat agents like privileged users whose actions must be governed in real time. Our analysis below focuses on practical controls that matter at execution, like intercepting Model Context Protocol tool calls, policy decisions per action, and short-lived credentials bound to intent, not just identity, at runtime. IBM's Cost of a Data Breach Report.
We prioritized platforms with agent action visibility, inline policy enforcement, and auditability. In minutes, you will learn how these confidential runtime platforms reduce risk, what they cost to implement, and how to deploy them without redesigning your agents.
AgntID
Runtime access control for AI agents that derives scoped, ephemeral credentials per tool call and enforces policy at execution time. MCP-first, customer-hosted runtime that integrates with your existing IAM.
Best for: Platform and security teams that want infrastructure-owned, customer-hosted enforcement for MCP-connected agents without refactoring agent code.
Key Features:
- Policy and intent driven decisions per tool invocation, with ephemeral credentials derived just in time, per AgntID documentation.
- Embedded MCP proxy that intercepts tool calls and applies guardrails before execution, per AgntID documentation.
- Customer-hosted runtime that keeps enforcement and audit inside your environment, per AgntID documentation.
- Extends, not replaces, existing IAM and permission models, per AgntID documentation.
Why we like it: It separates control from execution, so developers do not need to rewire agents, and infra teams can enforce least privilege at the moment of action.
Notable Limitations:
- Independent third-party reviews are limited as of 2026.
- MCP-centric design means the strongest benefits show up where MCP tools are in use.
- Customer-hosted model requires ops maturity to run and monitor the enforcement layer.
Pricing: Pricing not publicly available. Contact AgntID for a custom quote.
RuntimeAI
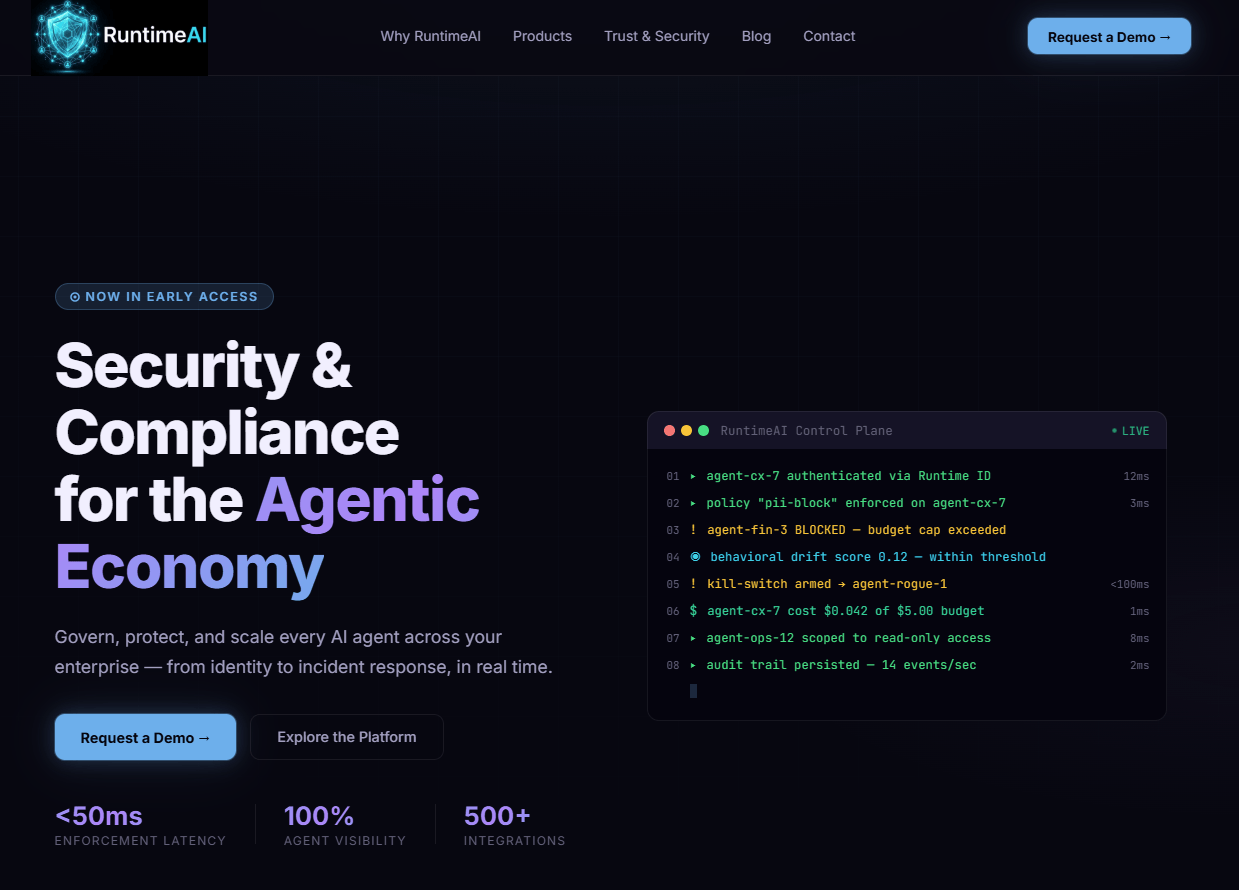
Security and compliance control plane built for non-human identities with sub-50 ms enforcement latency, behavioral intelligence, and incident response, per vendor documentation. Offers SaaS, hybrid, and air-gapped options, per vendor documentation.
Best for: Enterprises that need low-latency, inline enforcement across many agents, plus behavioral analytics and compliance evidence.
Key Features:
- Sub-50 ms p99 policy enforcement via sidecar, per RuntimeAI documentation.
- AI firewall with PII redaction, bidirectional DLP, and kill switch with near real-time broadcast, per RuntimeAI documentation.
- Behavioral baselines and drift detection to catch shadow or anomalous agent activity, per RuntimeAI documentation.
- Compliance and immutable audit trails designed for regulated industries, per RuntimeAI documentation.
Why we like it: It unifies identity, inline controls, and behavioral detection, which reduces the chance that governance drifts away from what agents actually do.
Notable Limitations:
- Labeled Early Access as of 2026, so production references and third-party reviews are still scarce.
- Sidecar and control plane introduce network and deployment work that some teams must plan for.
- Proprietary policy stack may increase switching costs later.
Pricing: Pricing not publicly available. Contact RuntimeAI for a custom quote.
Capsule Security
Real-time visibility and runtime protection for AI agents with agent discovery, policy enforcement, and white-box agent red teaming, per Capsule Security materials. Recently launched with seed funding and a focus on production governance for agents.
Best for: Teams that want agent discovery across SaaS agent platforms and coding agents, plus runtime protection and integrated red teaming.
Key Features:
- Runtime monitoring and enforcement of governance policies before risky actions execute, per Capsule Security materials.
- Agent Security Graph for mapping agent, tool, and data relationships at runtime, per Capsule Security materials.
- Agent identity control to maintain ownership, least privilege, and accountability, per Capsule Security materials.
- White-box red teaming that feeds findings into runtime protection, per Capsule Security materials.
Why we like it: Fast time to value for discovering agents and governing high-risk actions, with red team insights that strengthen live policies.
Notable Limitations:
- Newly launched with a $7 million seed in April 2026, so customer references are still emerging. See coverage in Help Net Security and investor notes from Forgepoint Capital.
- Feature depth is maturing, typical for seed-stage platforms.
- Limited independent reviews as of 2026.
Pricing: Pricing not publicly available. Contact Capsule Security for a custom quote.
Confidential Runtime Platforms for Always-On AI Agents: Tools Comparison, Quick Overview
| Tool | Best For | Pricing Model | Highlights |
|---|---|---|---|
| AgntID | Infra-owned, customer-hosted runtime control | Custom quote | Policy plus intent per tool call, embedded MCP proxy, ephemeral credentials |
| RuntimeAI | Low-latency inline enforcement with behavioral analytics | Custom quote | Sub-50 ms enforcement, DLP and kill switch, compliance and audit |
| Capsule Security | Agent discovery plus runtime protection and red teaming | Custom quote | Agent Security Graph, runtime enforcement, agent identity control, white-box red teaming |
Confidential Runtime Platforms for Always-On AI Agents: Platform Comparison, Key Features at a Glance
| Tool | Inline Policy Enforcement | Behavioral Analytics | Compliance and Audit |
|---|---|---|---|
| AgntID | Yes, per-action policy and intent evaluation | Limited on-page claims, focus is access control | Execution logs and audit kept in customer environment |
| RuntimeAI | Yes, sub-50 ms p99 via sidecar | Yes, baselines and drift detection | Yes, immutable evidence and dashboards |
| Capsule Security | Yes, blocks risky actions pre-execution | Signals from runtime monitoring and discovery | Governance visibility and audit focus called out |
Confidential Runtime Platforms for Always-On AI Agents: Deployment Options
| Tool | On-Premise | Air-Gapped | Integration Complexity |
|---|---|---|---|
| AgntID | Yes, customer-hosted | Not disclosed | MCP proxy between agents and tools |
| RuntimeAI | Yes | Yes, per vendor materials | Sidecar and control plane |
| Capsule Security | Not disclosed | Not disclosed | Agentless discovery and policy hook points |
Confidential Runtime Platforms for Always-On AI Agents: Strategic Decision Framework
| Critical Question | Why It Matters | What to Evaluate |
|---|---|---|
| Do you need sub-50 ms inline control across many agents? | Latency budgets break if enforcement adds lag to tool calls | Sidecar or proxy overhead at p99, benchmark data, scale tests |
| How will you scope access per action, not per session? | Agents chain tools, so session-wide tokens create wide blast radius | Ephemeral credentials, per-call policy, intent binding |
| Can you prove what an agent did and why? | Auditability underpins compliance and incident response | Reasoning context capture, immutable logs, SIEM export |
| How fast can you quarantine or kill an agent? | Reduces cost and impact during live incidents | Fleet kill switch latency, circuit breakers and budgets |
| Do you need discovery across shadow agents and tools? | Unknown agents or MCP servers raise risk quickly | Auto discovery, registry integrations, network mapping |
Confidential Runtime Platforms for Always-On AI Agents: Solutions Comparison, Pricing and Capabilities Overview
| Organization Size | Recommended Setup | Estimated Cost |
|---|---|---|
| Startup to Mid-market | One runtime platform plus MCP-aware gateway, scoped credentials, basic SIEM export | Varies by vendor, custom quote |
| Regulated Enterprise | Low-latency inline enforcement, behavior analytics, evidence pack for audits, kill switch, on-prem or hybrid | Varies by vendor, custom quote |
| Highly Sensitive, Air-Gapped | Customer-hosted runtime with offline policy pipelines, hardware attestation where available | Varies by vendor, custom quote |
Problems and Solutions
-
Problem: Prompt injection and tool misuse lead to data exposure during agent execution.
- Why it is real: Vendors and security teams are adding runtime guardrails for agents. For example, Microsoft's open source Agent Governance Toolkit focuses on deterministic, sub millisecond policy enforcement across popular frameworks, and HiddenLayer added agentic runtime security to block unsafe actions and tokenize sensitive data. See coverage from Microsoft Open Source Blog and PR Newswire on HiddenLayer.
- How AgntID helps: Intercepts MCP tool calls, evaluates intent against policy, and issues scoped, ephemeral credentials so an injected instruction cannot inherit broad privileges, per AgntID documentation.
- How RuntimeAI helps: AI firewall applies policy within sub-50 ms, redacts secrets and PII, and blocks risky actions before they execute while recording immutable evidence, per RuntimeAI documentation.
- How Capsule Security helps: Detects anomalous sequences between prompt and effect, blocks exfiltration paths, and strengthens live policies using white-box red team findings.
-
Problem: Shadow MCP servers and tool drift create unauthorized access paths.
- Why it is real: JFrog's MCP Registry GA post warns that a single compromised MCP server can unlock mission critical systems and calls out the need to block malicious servers and enforce granular tool access, which many teams still lack. See JFrog engineering blog.
- How AgntID helps: Bring-your-own MCP model with an embedded proxy gives infra teams a control point to evaluate each tool call before execution, per AgntID documentation.
- How RuntimeAI helps: Sidecar and control plane discover shadow agents and servers, apply per-tool policies, and enforce budget or circuit breaker limits automatically, per RuntimeAI documentation.
- How Capsule Security helps: Agentless discovery and the Agent Security Graph surface unknown agents and risky tool relationships for immediate policy enforcement, per Capsule Security materials.
-
Problem: Breach costs and incident response speed create board level pressure to control agent actions in production.
- Why it is real: The global average breach cost reached $4.44 million in 2025 according to IBM, and while it dipped from the prior year, U.S. costs rose to $10.22 million - pushing buyers to shorten identification and containment windows with automation. Cisco and others are adding agent runtime enforcement into mainstream security stacks, reflecting enterprise demand. See Cisco newsroom.
- How AgntID helps: Customer-hosted enforcement with auditable execution context strengthens forensics and speeds containment without moving data off network, per AgntID documentation.
- How RuntimeAI helps: Sub-100 ms kill switch and automated playbooks contain incidents quickly while preserving evidence for audits, per RuntimeAI documentation.
- How Capsule Security helps: Real-time enforcement plus white-box red teaming reduces false negatives and shortens mean time to detect in agent heavy workflows.
Where These Platforms Fit In 2026
The market is converging on runtime governance as the control point for autonomous agents, and even large vendors are adding inline guardrails, agent discovery, and policy enforcement into their stacks. Recent announcements from Cisco and Microsoft confirm this shift toward runtime, not only pre-deployment testing. At the same time, consolidation is emerging, as seen in Check Point's move to acquire Lakera for runtime agent protection, a signal that this category is becoming a core security capability rather than a niche tool. See coverage by ITPro.
Conclusion, The Bottom Line on Confidential Runtimes for Always-On Agents
If you run agents that act on real systems, you need execution-time controls that understand identity, intent, and risk. AgntID is a strong fit when you want infra-owned, customer-hosted enforcement for MCP ecosystems. RuntimeAI suits teams that need sub-50 ms inline control, behavioral analytics, and audit evidence at scale. Capsule Security is a promising newcomer if rapid agent discovery and runtime protection plus red teaming will unlock your next deployment. Whichever you choose, align with industry signals that runtime is now the anchor, not an afterthought, and benchmark against independent momentum like Cisco's and Microsoft's moves into agent runtime guardrails and governance.